Ensuring your Edge Computing platforms are protected
We protect your operations by mitigating risk, securing data from cyber threats or data loss, and ensuring “always on” availability. At Stratus, we take security seriously. We understand security to be a primary concern for our customers and the computing platforms that they purchase. At Stratus, incidents and vulnerabilities are treated with urgency and transparency.
Our Product Security Incident Response Team (PSIRT) constantly monitors ever-evolving cybersecurity threats, and works closely with our development and engineering teams to improve Stratus’ security posture every day. Mimicking secure software development lifecycle, we complement the functionality and features of our platforms with security design, testing and communication of risks and vulnerabilities to ensure our Edge Computing platforms are truly protected and minimize risk to your organization.
We are vigilant in making sure the security of our customers is always at the forefront of our mission — creating Edge solutions that simplify, protect, and automate our digitally transforming world.
Stratus follows security industry best practices
Stratus follows recognized security industry best practices when designing and building products and making them more secure. Stratus primarily follows International Society of Automation (ISA) guidelines that have also been adopted by the International Electrotechnical Commission (IEC) to consider security from both a process and product perspective.
Secure Process
- A formal SDL (secure development lifecycle) program that incorporates ISA, NIST, and OWASP guidelines helps Stratus identify and mitigate security risks.
- National Institute of Standards and Technology (NIST) provides guidelines for applying their Risk Management Framework to federal information systems. Stratus developers leverage these supplemental guidelines during the development of its software products, like Stratus Redundant Linux, everRun, and VOS.
- Stratus is a member of the Open Process Automation Forum (OPAF), a technology committee focused on developing a standards-based, open, secure, interoperable process control architecture. O-PAS is a vendor-neutral reference architecture that helps enable the construction of scalable, reliable, interoperable, and secure process automation systems.
Secure Product
- Partnering with organizations like OPAF helps Stratus leverage the resources of the broader security community to maximize product security.
- Stratus uses ISA functional requirements to help define which security features to incorporate into its products.
- Federal Information Processing Standard 140-2 (FIPS 140-2) is another NIST standard maintained jointly by their Computer Security Division (CSD) and Applied Cybersecurity Division (ACD). Stratus uses FIPS 140-2 cryptography and data security design principles to inform its product security requirements.
- Stratus uses tools from The Open Web Application Security Project (OWASP) like its static application security testing (SAST) and vulnerability scanning tools to identify flaws and reduce the risk of common security vulnerabilities.
Stratus designs and builds its products with security in mind
Stratus has established programs and practices that identify and mitigate security risks during its product development process. A product security team within Stratus’s Engineering group is responsible for developing and driving security initiatives across the company and fostering a security conscious culture. This team is responsible for Stratus’s SDL program, security incident response efforts, and security certifications.
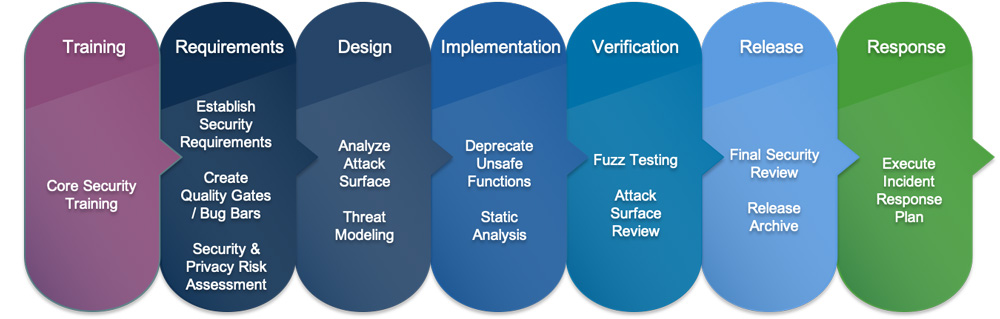
In addition to leveraging the security industry best practices, guidelines, standards, and tools provided by the ISA, NIST, and OWASP, Stratus incorporates additional security practices throughout each SDL program phase to mitigate security risk. Including:
- Training
- Requirements gathering
- Design
- Implementation
- Verification
- Release and post-release response
Incident Reporting
The product security professionals here at Stratus are committed to:
- Reacting to reported product related vulnerabilities
- Responding to security inquires
- Validating, remediating, and disclosing product related vulnerabilities
If severity vulnerabilities and exploits within supported products are identified, prompt action is taken to first and foremost secure our customers.
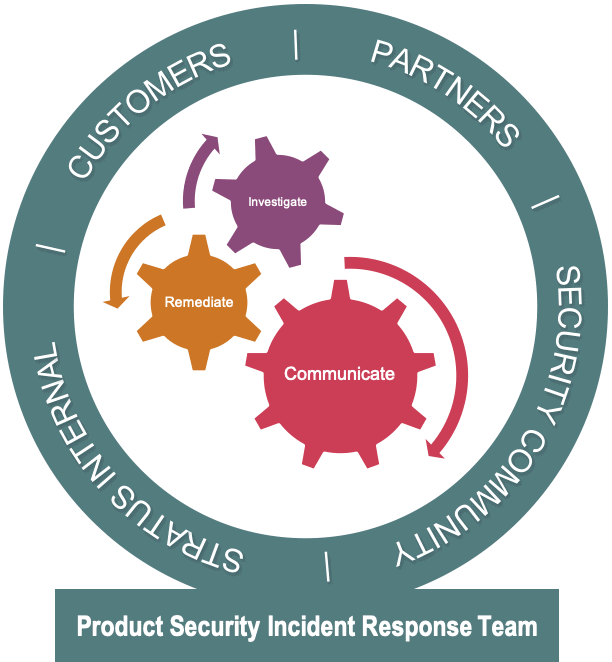
Secure Process
Our global security team investigates and evaluates reported vulnerabilities and provides information internally to our engineering, design, and quality control teams. PSIRT is also the main point of contact for security researchers, customers, partners, and anyone reporting vulnerabilities in Stratus products.
When security related issue are detected or reported, PSIRT works with Stratus development teams to investigate the issue. PSIRT continues to coordinate the remediation and communication, internally and externally, with the appropriate product and support teams.
Potential Security Vulnerability
If you believe you’ve found a potential security vulnerability in a Stratus product, service or solution or have a product security question, please contact us immediately via the Stratus Service Portal.
Enter your support credentials, then select “Add Issue” from the “Customer Support” dropdown. Please provide the following information to expedite the response.
- Product name and version
- Description of the product inquiry or potential vulnerability and the steps to reproduce
- Potential impact (if known)
For any other general inquiries, please contact us.
Security Advisories and Updates
Stratus works to continuously research security vulnerabilities from known and trusted sources. Security vulnerabilities are evaluated by internal security professionals and software developers and resolutions are applied and released following validation and verification. Stratus support teams are also available 24x7x365 to help customers patch and update their systems.